CBOM and Cryptographic Inventory: The Two Essential Layers of Cryptographic Visibility
CBOM and cryptographic inventory sound similar but answer different questions. One shows what's built in; the other shows what's actually in use.

Most organizations are now being asked to build a Cryptographic Bill of Materials (CBOM) and manage a “cryptographic inventory.” While these two things may sound similar or sometimes used interchangeably, they are, in fact, quite different. It is important to understand their purposes and applications as they provide answers to different questions, operate at distinct layers, and their accuracy varies based on unique factors. Understanding the distinctions between these two things is important for minimizing cryptographic visibility gaps in your organization. One record describes what should exist, and the other reflects what actually does.
CBOM vs. Cryptographic Inventory at a Glance
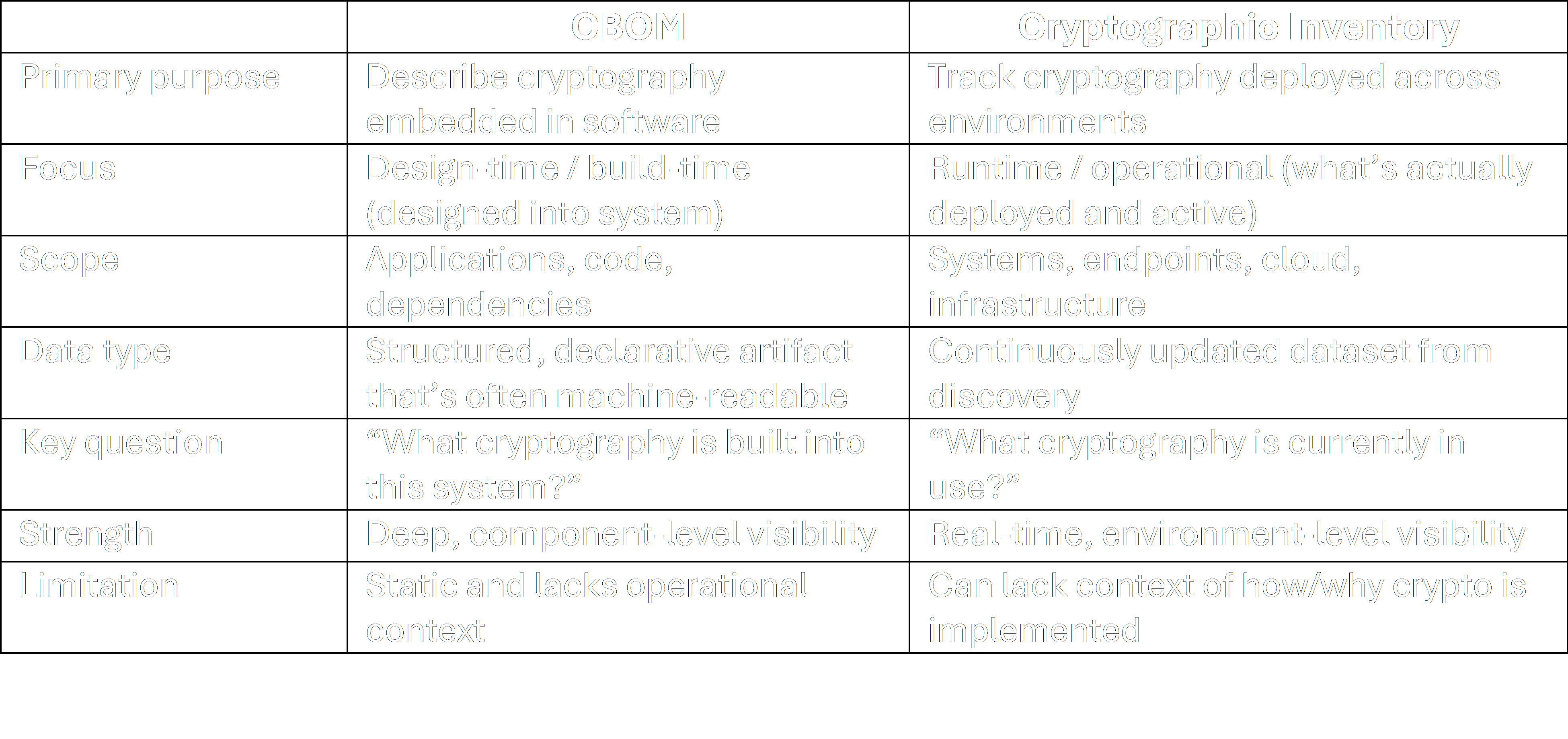
A Cryptographic Bill of Materials (CBOM) is a structured record of the cryptography inside a system. This includes algorithms, keys, certificates, protocols etc., and how they relate to software components. A CBOM builds on the Software Bill of Materials (SBOM) model but focuses specifically on cryptographic elements and how they interconnect. In practice, a CBOM is most useful for understanding exposure at the design level since it tracks which algorithms are in use, where deprecated primitives exist, and what things must change in pursuit of post-quantum readiness. But it’s inherently static, making a CBOM’s effectiveness decrease as systems change after deployment. This happens when the inventory lags and, therefore, doesn’t reflect the present. It reflects what the software is capable of using but not necessarily how it’s configured or deployed in a given environment.
A cryptographic inventory, by contrast, is an operational view. It answers a simpler but harder question: what cryptography actually exists across the environment right now? Think: certificates on endpoints, keys in HSMs, libraries in running workloads, and protocols in active use. A cryptographic inventory is typically built via continuous discovery rather than generated as a file or artifact. Where a CBOM tells you that a system supports a given algorithm, an inventory shows whether it’s actually in use (and where). The primary benefits are that it supports prioritization, remediation, response, and ongoing control at scale. For a cryptographic inventory to be useful to an organization, an evaluation of its cryptographic landscape must be ongoing, rather than a point in time. Inventories lose accuracy when discovery isn’t continuous, ownership is unclear, or updates to certificates, keys, and services aren’t reflected in near real time.
How They Complement One Another
While quite different, the two intersect. For example, a CBOM can tell you that a service depends on a vulnerable algorithm, while an inventory can tell you which instances of that service are actively using it. A CBOM provides structure and traceability. An inventory provides state and coverage. Without the CBOM, the inventory lacks context. Without the inventory, the CBOM lacks reality. Most of the friction organizations experience, especially around crypto-agility, stems from trying to operate with only one of these views.
Where to Begin?
If your organization needs to develop both a CBOM and a cryptographic inventory, starting with the cryptographic inventory may be the most useful, even if this feels counterintuitive. This is because it’s difficult to manage or prioritize what you can’t see, and inventory establishes the current state. From there, a CBOM becomes more useful since it explains dependencies and supports longer-term transitions like algorithm migration. Ultimately, the order matters less than the end state, since both are required. What matters over time is not the artifacts themselves, but how closely they reflect reality as it changes. The gap between those two views is where response slows down, leaving an organization more vulnerable to threats.
Ready to conduct a cryptographic inventory? Schedule a discovery call with us.
Nail down the essentials: Download our white paper to learn more about Cryptographic Posture Management and determine if your organization is quantum resilient.
Subscribe to our weekly newsletter
Receive weekly insights on cryptographic risks, emerging security standards and quantum readiness.



