Cryptographic Discovery
Qinsight simplifies discovery so teams can eliminate blind spots and understand the true footprint of their cryptography.
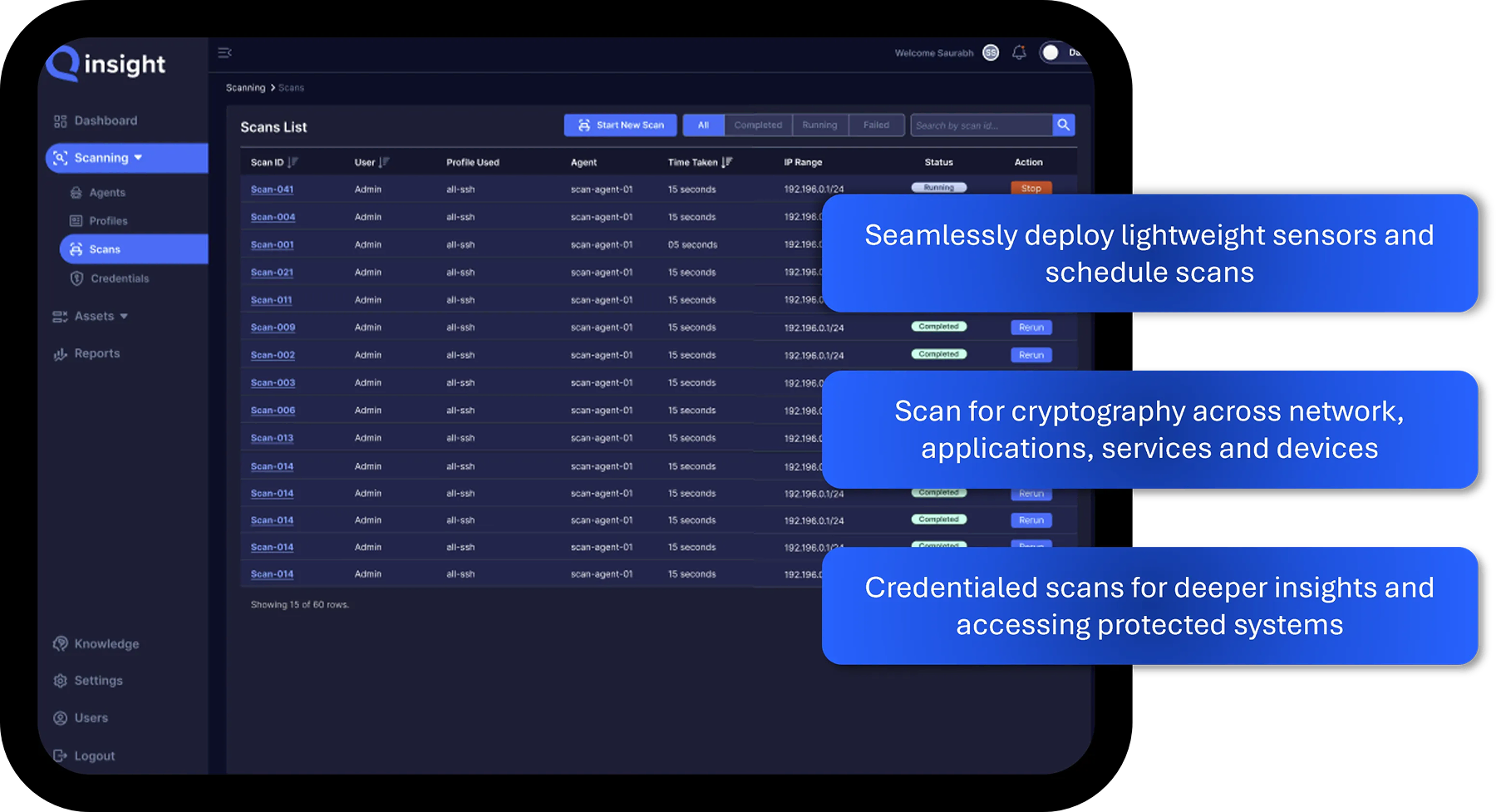
Scale and Automate The Cryptographic Discovery Process
Discover cryptographic assets across networks, cloud, infrastructure, and the software supply chain.
Atlas combines network scans, credentialed scans, and APIs to inventory crypto in motion and at rest — deploying through systems already standard in the enterprise.

Improve Cryptographic Posture
Full Visibility
Gain complete insight into all cryptographic assets across your enterprise environment.
Continuous Monitoring
Detect changes in cryptography in real-time to maintain ongoing protection and compliance.
Improve Security
Identify weak or expired encryption, keys, and certificates before they become exploitable.
Reduce Downtime
Prevent service outages by proactively managing expiring certificates and crypto dependencies.
Quantum Readiness
Assess exposures to quantum-vulnerable algorithms and plan migration to post-quantum standards.
Ensure Compliance
Meet evolving regulatory and industry mandates like PCI-DSS and CNSA 2.0 with customized policies and reporting.
How Qinsight Atlas Discovery Process Works
Two step discovery process to ensure maximum reach and depth of insights across data sources.

Deploy Sensors Across Network Segments
Deploy sensors either directly or through a proxy connection within each network segment. Collect network cryptography and discover applications and services where credentialed scans are necessary.

Connect to Source Types and Add Credentials
Findings are normalized into a searchable CBOM with algorithms, key sizes, certificate chains/issuers/expirations, protocol/cipher details, systems, and owners — ready to tag and export.
Schedule Scans for Continuous Monitoring
Policy checks flag weak/expired/non-standard crypto, deprecated protocols, short keys, and quantum-susceptible usage. Analyze quantum readiness, and export compliance-ready reports.
