47-Day TLS/SSL Certificates: The Operational Impact of Shorter Lifecycles
The CA/Browser Forum is compressing TLS certificate lifecycles to 47 days by 2029. Organizations must rethink certificate management, starting with visibility into what they have.
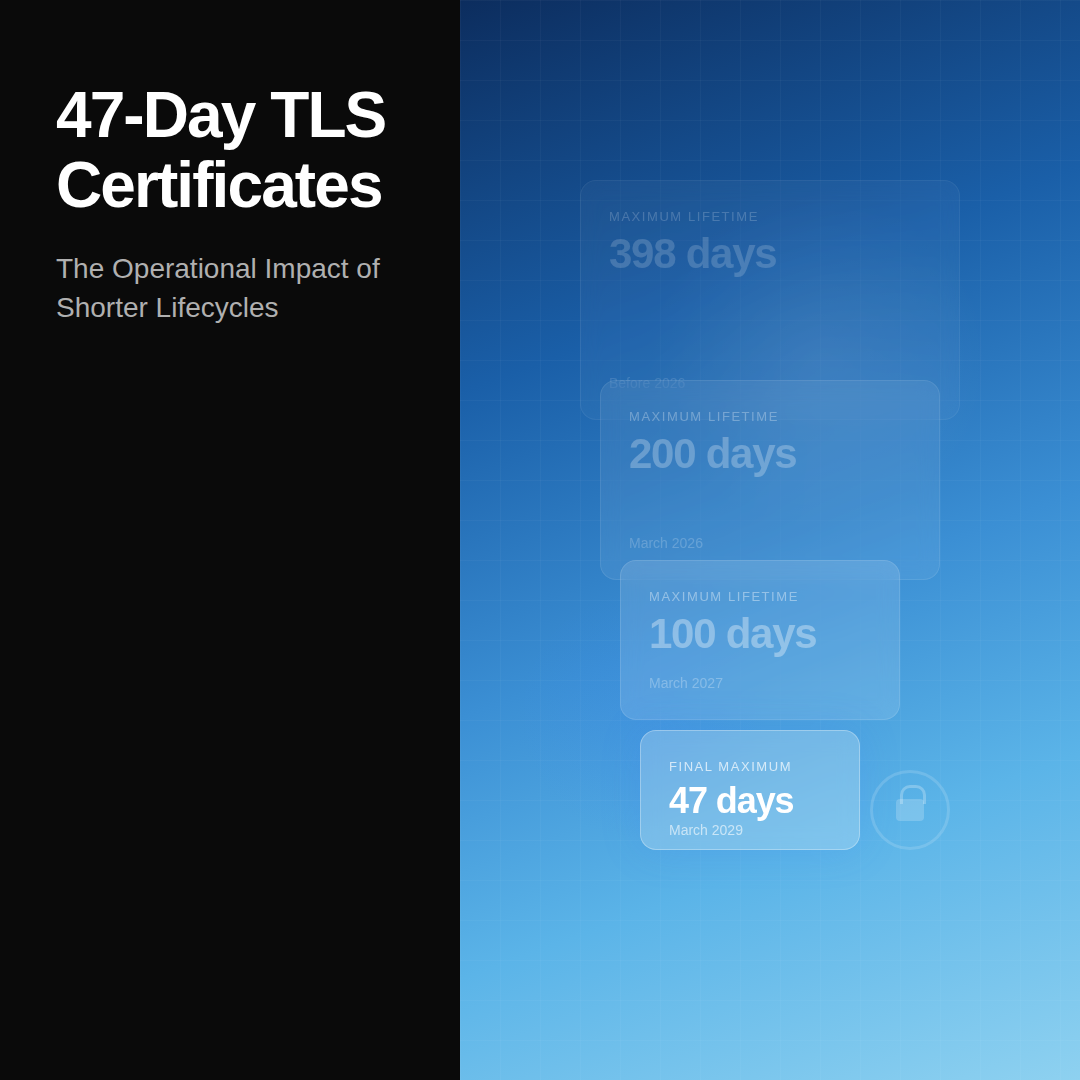
The CA/Browser Forum recently passed a phased mandate to reduce the maximum lifetime of public TLS/SSL certificates. The rollout follows an aggressive timeline: a 200-day maximum by March 2026, a 100-day maximum by March 2027, and a final 47-day maximum by March 15, 2029. This shift to six-week lifecycles is designed to enhance security and force the adoption of automation.

As far more than simply a technical standards update, this new phased mandate indicates a broader shift in how the security industry is approaching digital "trust." In the past, certificate lifecycles were long enough that organizations could rely on a mix of manual processes, partial visibility, and unclear ownership. This will have to evolve to meet the requirements of this mandate. With the validity window shrinking from over a year to roughly a month and a half, organizations must spend the next few years revamping their certificate management requirements. The end goal is a management approach that involves continuous, automated certificate evaluation rather than an ad hoc analysis.
For CISOs, the impact of this mandate has clear implications for how certificate operations must run day to day. Compressing lifespans reduces exposure, but it also increases the volume and frequency of lifecycle events like issuance, deployment, rotation, and validation. That shift will further compound pre-existing "weak" spots, which may involve unclear ownership, incomplete inventory, inconsistent renewal processes, and lack of an overall governance structure. If left unaddressed, organizations may see missed renewals, failed deployments, and outages that are harder to predict and faster to repeat. This can quickly erode organization trust and mitigation can be costly.
Many organizations already experience a degree of friction in the complex landscape of their certificates. Certificates are scattered across cloud services, internal infrastructure, third-party platforms, and increasingly short-lived workloads. It's common for teams to rely on spreadsheets, ticketing systems, or institutional knowledge to keep track of what exists and when it expires. Under a 47-day model, those same gaps are hit more often, and with less time to recover. What used to be an occasional oversight can quickly become a recurring issue.
Also read: The Foundation of Digital Trust
This is where the conversation shifts from certificates to operating model. Managing shorter lifecycles at a large scale that many enterprises will require demands a clear understanding of what exists, who is responsible for it, and how it is maintained over time. It also requires reducing dependence on manual steps that don’t scale with frequency. The goal isn’t just to renew certificates faster, but to make the process predictable and resilient, even as the pace increases.
This mandate will accelerate adoption of Certificate Lifecycle Management (CLM) solutions, platforms designed to automate the full certificate lifecycle from issuance through renewal and revocation. For organizations managing thousands of certificates across hybrid environments, CLM becomes essential infrastructure rather than a nice-to-have. But CLM solutions are only as effective as the inventory they operate on. If your organization doesn't have complete visibility into where certificates live, who owns them, and what systems depend on them, automating renewal on a 47-day cycle risks compounding errors at scale rather than preventing them. Discovery and inventory must come before automation.
It's also worth noting that the 47-day certificate deadline converges with Google's recently announced 2029 PQC migration target. The fact that both hit the same year isn't coincidental: organizations will need to manage dramatically shorter certificate lifecycles at the same time they're migrating those certificates to post-quantum algorithms. This convergence reinforces why crypto-agility is no longer aspirational, it's operational.
Learn more about crypto-agility
Ultimately, 47-day certificates indicate a move toward continuous trust, where security isn't only checked once a year. Underlying certificate governance must change, and, with this, risk gaps will be exposed and must be addressed. For CISOs, it's a useful moment to take stock: not just of whether the organization is ready for shorter lifetimes, but if its current approach to managing cryptographic risk can keep up with where the industry is heading.
Build Your Certificate Visibility Foundation with Qinsight Atlas

Shortening certificate lifecycles means more frequent lifecycle events across a larger, more complex estate. Without complete visibility into where certificates exist, their expiration status, and who owns them, organizations risk turning a security improvement into an operational liability. Qinsight Atlas discovers and inventories certificates alongside every other cryptographic asset in your environment, giving you the foundation to manage shorter lifecycles with confidence. Learn more at qinsight.com.
Subscribe to our weekly newsletter
Receive weekly insights on cryptographic risks, emerging security standards and quantum readiness.