The Q-Day Countdown: Google’s Latest Announcement
Google's 2029 PQC deadline signals the quantum threat timeline is accelerating. Organizations must start cryptographic discovery and migration now

Google’s latest quantum announcement, which came on March 25, 2026, sparked a sense of urgency for post-quantum readiness. Long regarded as a “marathon,” Google shifted the tone of the post-quantum computing (PQC) conversation towards a “sprint.”
Google’s PQC Migration Plan
Google disclosed that work is underway to complete its migration to post-quantum cryptography by 2029, a good five years sooner than what many sources, such as NIST and McKinsey, cited as the target migration date and quantum’s maturity point as of 2035.
Google called out three key areas of rapid advancement that led to announcing its “ambitious timeline”: (1) quantum hardware acceleration, (2) error correction advances, and (3) factoring estimates. Google’s VP of Security Engineering writes, “We hope to provide the clarity and urgency needed to accelerate digital transitions.” Google’s example is not just one for its industry; quantum risk and a proactive PQC strategy are sector-agnostic and enterprises should take notes.
Key Implications of a 2029 PQC Migration Plan:
- This announcement is not about predicting a specific Q-day; rather, it underscores the importance of executing a PQC strategy in the near term. Google’s article is, fundamentally, a governance signal and indicates that quantum readiness belongs to an enterprise risk management system. As observed over the last few years, this preparation window continues to shorten compared to what many leaders originally estimated. Organizations with hard-wired cryptography will struggle to respond quickly when timelines tighten again. This is why crypto-agility is now a boardroom topic.
- With quantum computing capabilities, critical information, financial transactions, and global systems could potentially be undermined at scale. Migration priorities may look different from sector to sector, but the fundamental challenge is the same. Cryptography spans applications, vendors, infrastructure, devices, certificates, and signing systems. This innate complexity is further complicated by the fact that this library of cryptography often lacks clear ownership, and an exhaustive cryptographic inventory hasn’t been performed. Learn the basics of performing a cryptographic inventory.
- Migration to post-quantum cryptography is not just another routine technical update, and the focal point should not just be the deadline. Attackers already have the ability to collect protected data and store it until it becomes readable later. Trust and reputational risk are already on the line. When that happens, even a well-understood security requirement turns into a slow, expensive transformation. Learn more about Harvest Now, Decrypt Later (HNDL).
Practical next steps for organizations
- Complete a full cryptographic inventory of keys, certificates, protocols, algorithms, secrets and dependencies across applications, infrastructure, code repositories, devices and vendor dependencies.
- Establish executive ownership and a steering committee. Include representation from your organization’s legal, audit, procurement, and product teams so the effort is run as an enterprise program.
- Develop a roadmap to prioritize systems based on data sensitivity, data life span, business criticality, and reliance on digital signatures or authentication.
- Require essential vendors and service providers to disclose their own post-quantum risks (e.g., cryptographic dependencies) and migration planning.
- Where possible, design for flexibility by separating cryptography from application logic. This will help reduce future migration costs.
Sector-specific priorities
Financial services
- Key areas of concern: Identify payment, settlement, trading, and identity systems that depend on long-lived keys, certificates, and signatures.
- Prioritize: Migrating data and transactions that carry long retention periods or regulatory exposure, including archived customer and market records.
- Action: Add quantum-readiness proof to vendor requirements for core banking, capital markets, payments, and custody platforms.
Healthcare
- Key areas of concern: Patient records, genomic data, medical imaging, and other information with long-term sensitivity.
- Prioritize: Understanding exposure across connected devices, clinical platforms, and any third-party vendors where embedded cryptography may be difficult to update.
- Action: Develop a phased roadmap for identity, access, and signing controls that support care delivery without disrupting essential operations.
Government and public sector
- Key areas of concern: Personally identifiable information (PII), classified data, mission-critical data, long-retention records, etc.
- Prioritize: Treating post-quantum readiness as a continuity and trust issue, not only a cybersecurity initiative. Signature integrity and authentication failure can affect core public services.
- Action: Evaluate legacy infrastructure dependency where cryptography may have limited visibility and governance and where data migration may be a significant lift.
Summary
Google's 2029 migration deadline is the latest signal that the post-quantum timeline is compressing, not expanding. What was once framed as a 2035 horizon has shortened by half a decade in just a few years, and there is no reason to believe this trend will reverse. The reality is that PQC migration is a multi-year effort that touches every layer of an enterprise: applications, infrastructure, vendors, devices, and signing systems.
Organizations that wait for timeline certainty before acting will find themselves in crisis-mode migration when the window tightens again. The time to begin is now, starting with a comprehensive cryptographic inventory, executive ownership, and a risk-prioritized roadmap. The organizations that move early will move cheaply. The rest will be playing catch-up against a deadline that keeps getting closer.
Start Building a Cryptographic Inventory Today, with Qinsight Atlas
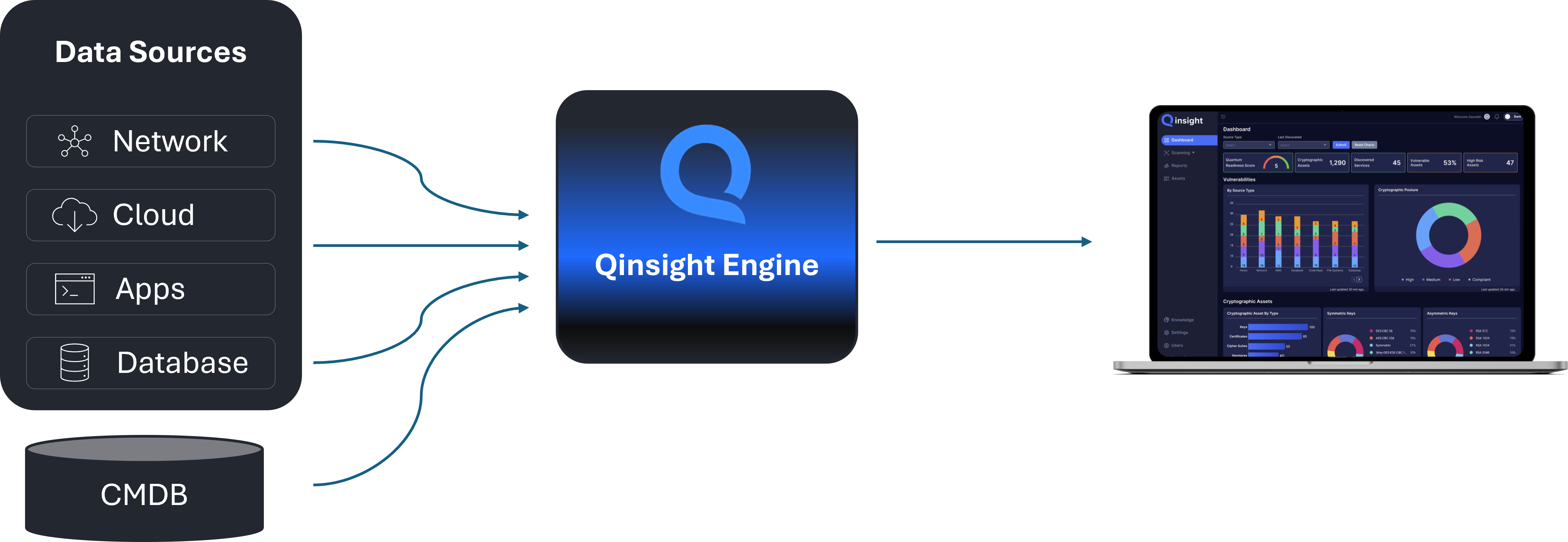
The first step in any PQC migration is understanding what cryptography you're running and where it lives. Qinsight Atlas discovers and inventories cryptographic assets across your enterprise, generates a Cryptographic Bill of Materials, and scores your quantum risk so you can prioritize what to migrate first. Start your quantum readiness journey at qinsight.com.
Subscribe to our weekly newsletter
Receive weekly insights on cryptographic risks, emerging security standards and quantum readiness.


.png)